The Credential Layer
Why a Compromised Card Number Defeats Every Layer Built to Stop It
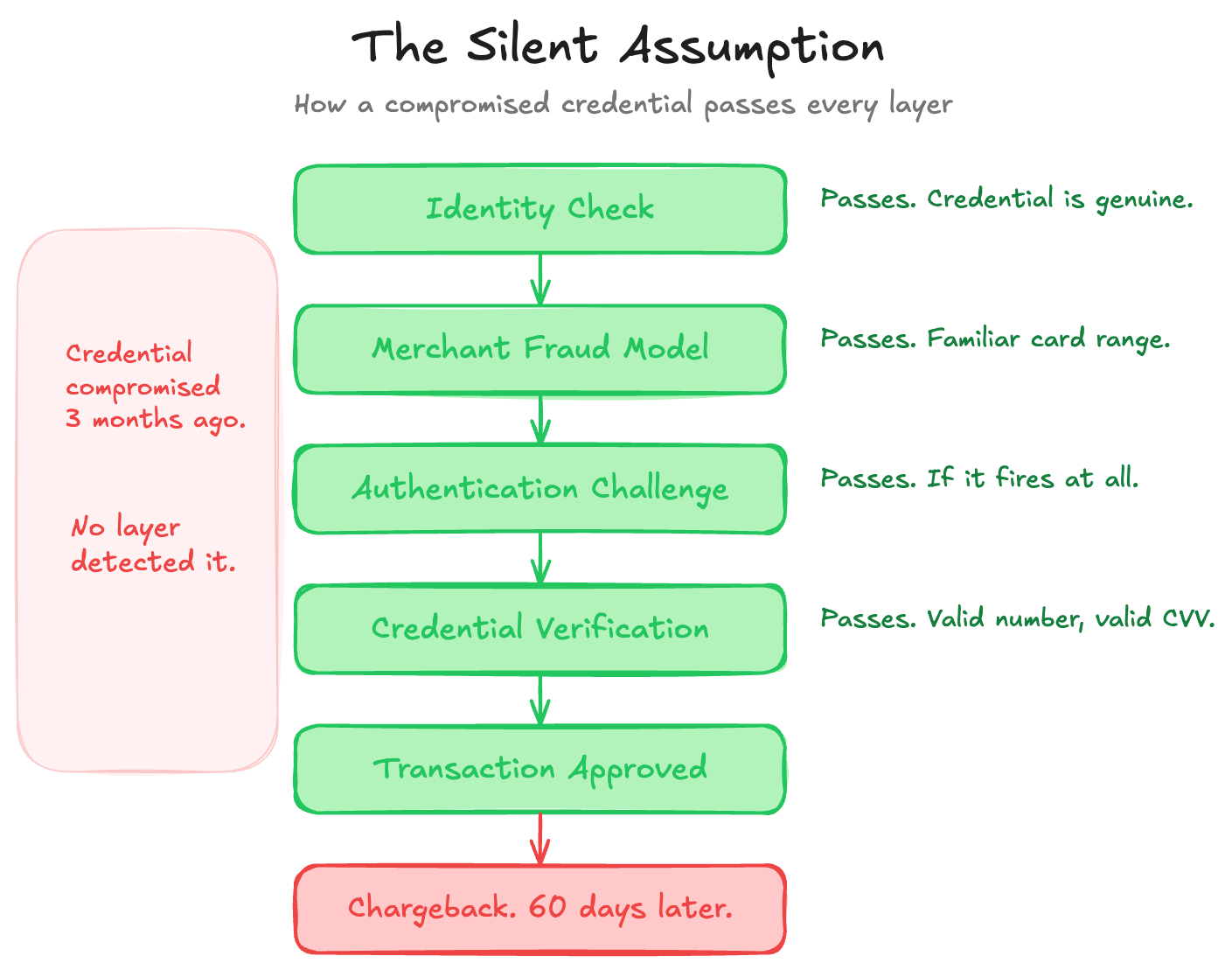
Every layer of the risk stack makes the same silent assumption. The credential is real.
The identity check verifies who is transacting. The merchant’s fraud model scores the session against hundreds of signals. The authentication challenge tests the claim.
Each layer does real work with real data. And each layer trusts that the credential being presented wasn’t compromised three months ago in a breach that the issuer hasn’t yet detected. When that trust is misplaced, every correct decision above it produces the wrong outcome. The identity check passes because the credential is genuine. The merchant’s fraud model sees a familiar card range on a returning customer’s device. The authentication challenge succeeds if it fires at all. The transaction clears. The merchant ships. The chargeback arrives sixty days later.
The Identity Theft Resource Center recorded 3,158 US data compromises in 2024, with roughly 1.7 billion victim notices driven by six mega-breaches, including Ticketmaster, Change Healthcare, and AT&T. Stolen credentials were the leading attack vector in cyberattacks on publicly traded companies that year. Four of the six mega-breaches were credential-driven.
Tens to hundreds of millions of stolen card records circulate on dark web marketplaces at any given time, priced at roughly $5 to $15 per card. According to Recorded Future’s lifecycle analysis, a compromised card is typically used for fraud within three to four days of purchase, after a checker-service validation step that costs 20 cents. The credential layer is the foundation of every trust decision in the stack. It’s also the layer the industry treated as solved while it was quietly becoming the weakest link.
The Architecture Built for Plastic
The Primary Account Number, the long card number printed on the front, is a permanent, reusable, non-revocable identifier. It was designed for a world of plastic cards and carbon-copy imprinters. It was never designed to be stored in merchant databases, embedded in recurring-billing engines, or typed into browsers. But that’s exactly what happened. The PAN became the default key for card-on-file storage, subscription billing, and every card-not-present transaction the e-commerce economy runs on. A static identifier, permanently bound to an account, is replicated across every merchant that has ever stored it.
The Card Verification Value is a three-digit static secret printed on the back of the card. PCI DSS prohibits storing it after authorization. Breaches continue to surface CVV alongside PAN anyway, because compliance is a posture, not a guarantee.
The CVV has two structural weaknesses that I want to name directly. The first is the Newcastle University Distributed Guessing Attack, published in 2016. Researchers demonstrated that with a valid PAN, an attacker can recover the expiry date in roughly 60 guesses and the CVV in under 1,000 guesses by distributing attempts across hundreds of e-commerce sites. Each site enforces its own lockout threshold. None of them shares velocity data with the others. The attack recovered a full set of card credentials in under six seconds. The original research found Visa’s network vulnerable. Mastercard’s centralized detection caught it within roughly ten attempts, even when distributed. No public scheme statement claims this structural weakness has been closed. The global web security community (OWASP) still lists card cracking as an ongoing automated threat in 2026.
The second weakness is simpler. The CVV isn’t required for all online card transactions. Recurring payments, subscriptions, merchant-initiated charges, and some tokenized flows don’t require it. The three-digit code on the back of your card doesn’t even cover the full range of online card usage.
The credential architecture was built for a world where a human holds a card, physically presents it, and the static values on it are secret. Two of those three assumptions are already gone. The third is under structural pressure from a direction the original architects never anticipated.
The card industry’s security standard, PCI DSS 4.0, had its latest requirements take effect on March 31, 2025. It tightened controls around how card data is stored, transmitted, and accessed. No public compliance rate has been published since the deadline passed. The standard itself is rigorous. But the enforcement model relies on self-assessment for most merchants and third-party auditing only for the largest. PCI measures whether organizations have the right controls in place. It does not measure whether those controls actually prevent card data from being stolen. The distinction matters. Every major breach that surfaced card credentials in the ITRC dataset occurred at an organization that was, at the time of the breach, either PCI-compliant or in the process of attesting to compliance.
The Rotation Spectrum
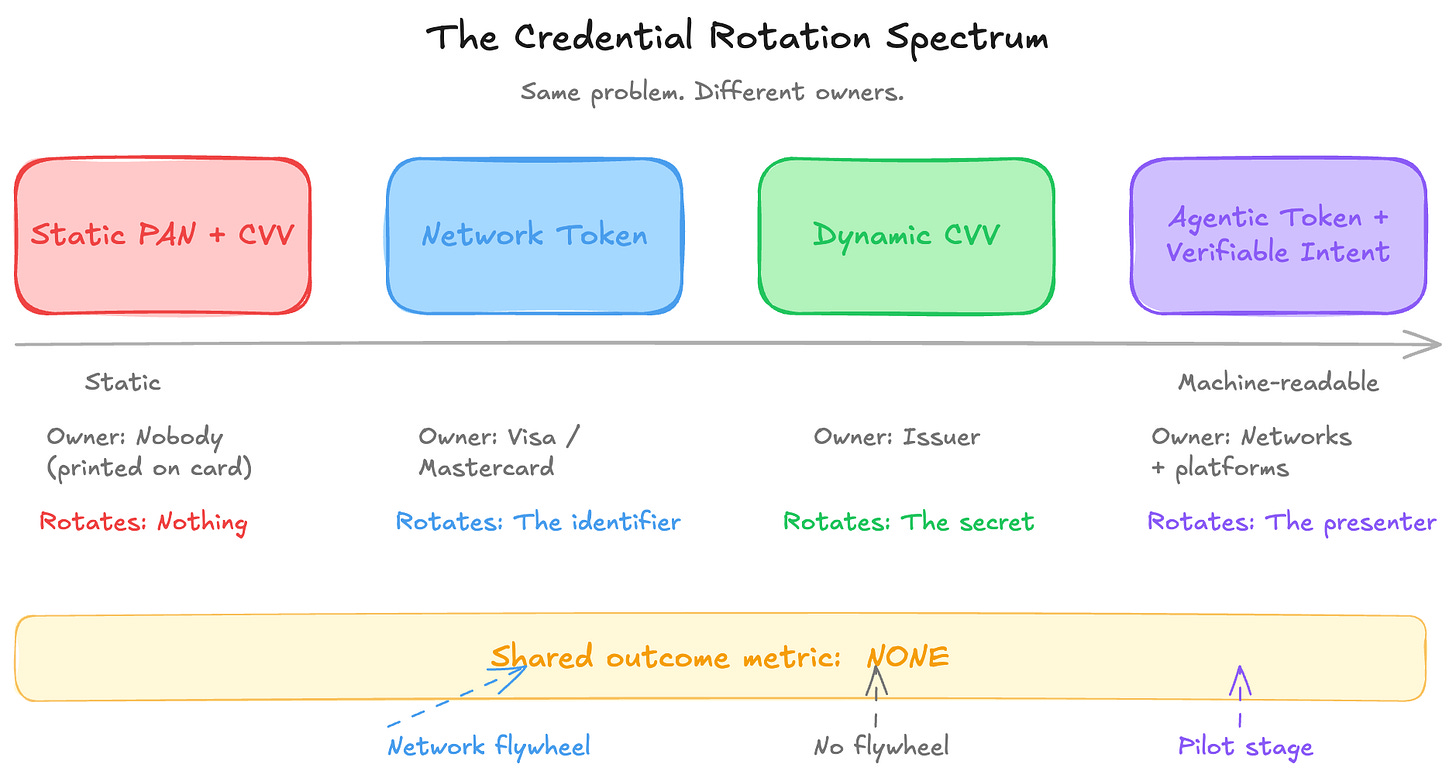
The industry’s answer to the static-credential problem comes in two forms. Both are attempts to stop trusting static values. They sit at different points on the same architectural spectrum, are deployed by different actors, and operate under different economic models. Neither was designed to complement the other.
Network tokenization is the dominant response. Instead of sending a card’s real number to the merchant, the network replaces it with a token that only works for that specific merchant or channel. If the token gets stolen, it’s useless elsewhere. Visa reported 13.7 billion tokens issued cumulatively as of late 2025, with roughly 50% of Visa's global e-commerce transactions now using tokens instead of real card numbers. Mastercard reported that roughly 35% of all transactions would be tokenized by mid-2025.
Both networks frame tokenization as a Value-Added Services revenue line and disclose growth rates that outpace those of core processing revenue. Visa reports a 28-40% reduction in fraud for tokenized versus non-tokenized online transactions, depending on the analysis window. Mastercard reports similar directional improvement. Both figures are network-published and should be read accordingly.
Tokenization has made the credential layer meaningfully better. But it hasn’t made it honest. The real card number still exists in the network’s vault. The token is a stand-in, not a fix for the underlying architecture. And it creates a downstream effect the industry hasn’t fully reckoned with. When a token is present, the bank’s fraud-scoring system treats the transaction as more trustworthy. The merchant’s fraud model relaxes too. The token looks clean, so the authorization looks clean, so the approval comes through. That’s the right outcome when the underlying customer is legitimate. When they aren’t, when the account was opened with a fake identity or has been taken over, tokenization actually makes the fraud harder to catch because the token itself is genuine. The same mechanism that helps legitimate customers can help a bad actor who controls a valid card.
A Visa token can’t be used on the Mastercard rail. Cross-network tokenization remains fragmented. India’s Reserve Bank mandated tokenization in October 2022, banning merchants from storing raw card numbers and pushing adoption of tokenization on consumer devices and bank-side vaults. It’s the only major market where a regulator forced tokenization as a baseline rather than leaving it to commercial incentives. Everywhere else, tokenization adoption is voluntary, commercially driven, and accelerating inside each network while interoperability across networks remains unresolved.
Dynamic credential rotation is the other architecture. It replaces the static printed CVV with a dynamic value. Two deployment models exist. Card-side display puts an e-paper screen on the back of the card, refreshing the code every one to four hours. IDEMIA’s MOTION CODE has been deployed across issuer programs in France, Spain, and Malaysia, as well as embedded-finance platforms, with over 600,000 cards issued by 2018. App-side generation produces a biometric-protected dynamic code through the issuer’s mobile banking app.
SafeCypher’s deployment with An Post Money in Ireland is the most publicly documented example of this model, with An Post and SafeCypher jointly reporting no CNP fraud through the An Post Money App over an 18-month period.
IDEMIA has published a similar zero-CNP-fraud claim across its MOTION CODE deployments. Both claims are vendor-issued. The transaction volume denominators are not publicly disclosed. The structural argument doesn’t rest on zero-fraud claims. A rotating secret tied to a separate channel collapses the three- to four-day breach-to-fraud reuse window that makes stolen static credentials monetizable. That argument is independently defensible.
The gap between these two architectures isn’t technical. It’s commercial. Tokenization sits inside the networks’ Value-Added Services revenue lines. Visa and Mastercard report token growth to investors. Dynamic CVV is an issuer-side cost with no network revenue share. No US top-25 issuer by card volume has publicly disclosed at-scale dynamic CVV deployment. The technology is mature. The barriers are commercial, not technical. The credential layer’s two responses to the same structural problem are deployed by different actors with different economics, and the one with the network flywheel is winning.
Both are points on the same spectrum. A network token is a long-lived, rotating identifier. A dynamic CVV is a short-lived rotating secret. Neither was designed to complement the other. Neither addresses what happens when the entity presenting the credential isn’t human. And neither is measured against a common outcome metric. The credential layer has two partial answers, two different owners, and no shared measurement of whether either one is working at the system level.
When the Presenter Isn’t Human
The credential model was designed for a human typing a card number into a browser or tapping a card against a terminal. That assumption is under structural pressure from AI agents, software that can browse, compare, and buy on behalf of a human, which are beginning to initiate transactions without the cardholder being present at all.
Visa launched its Trusted Agent Protocol in October 2025 with Cloudflare and twelve launch partners, including Adyen, Stripe, Worldpay, and Shopify. TAP is open-spec, published on GitHub, and uses HTTP Message Signatures with a Visa-operated public-key directory to carry Agent Intent, Consumer Recognition, and Payment Information. No money moves over TAP itself. It’s an identity-of-agent layer that composes with the existing payment rails.
Mastercard introduced Agent Pay in April 2025, extending its tokenization infrastructure with Agentic Tokens. The September 2025 expansion added Insight Tokens for permissioned data-sharing and Verifiable Intent for transaction-level authorization. Google’s Agent Payments Protocol (AP2) has sixty-plus coalition members, including Mastercard, Visa, PayPal, Stripe, and American Express, and is live with select merchants. EMVCo acknowledged in November 2025 that its specifications for 3DS, Payment Tokenization, and SRC need to be developed and enhanced for agentic payments. That acknowledgment is itself the evidence. The layers were not designed to compose.
These are real efforts at a real problem. TAP, Agent Pay, AP2, and EMVCo’s emerging workstream are all attempts to retrofit the missing system layer onto a stack that was never designed to compose. But the list of what hasn’t been solved is longer than the list of what has.
Who pays when an agent makes a purchase that the customer didn’t authorize?
That remains formally unresolved at the scheme level. The payment message format that banks use to talk to each other, a standard designed decades ago, has no field for “this transaction was initiated by an AI agent acting on behalf of this person.” How fraud-detection models should interpret software behavior rather than human behavior remains unresolved. No regulator in India, Singapore, Australia, Japan, or Hong Kong has published a public position on agent-initiated payments specifically.
The credential-rotation spectrum directly surfaces this tension. A dynamic CVV on a physical card requires a human to read a code. That’s fundamentally incompatible with an AI agent making a purchase. An app-generated dynamic CVV with biometric approval could, in theory, work with delegated agent flows, but no one’s tested it in production. Network tokens, because they’re already digital and machine-readable, naturally compose with agent-initiated payments. Agentic Tokens are explicitly built on that foundation. The credential architecture that’s winning on commercial adoption is also the one that works with the agentic future. The architecture with the stronger argument against breach-driven fraud may not survive the transition to machine-initiated payments.
The regulatory picture is equally unresolved. Europe’s upcoming PSD3 regulation includes expanded liability for payment providers when customers are defrauded through impersonation, but doesn’t specifically address agent-initiated payments. The US has no equivalent federal mandate. The gap between where regulators are and where the technology is heading is measured in years.
The volume reality is honest about where this stands. As of late 2025, Visa reported “hundreds” of completed agent-initiated transactions across all production partners. The forecast is millions by the 2026 holiday season. That’s a forecast, not a fact. The structural break is real. The commercial volume is still measured in pilots.
The Layer Nobody Measures
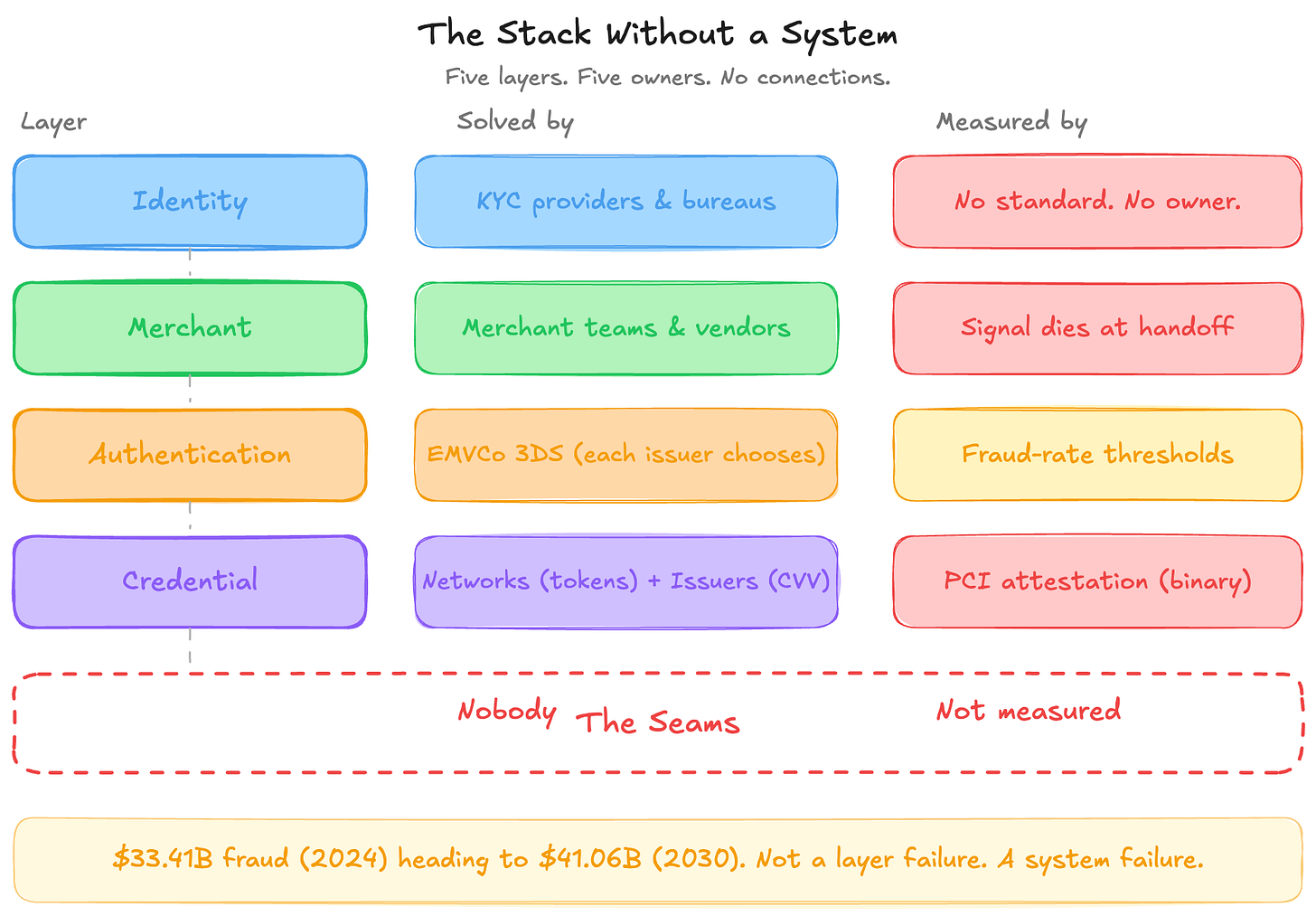
Every other layer in the risk stack has a measurement regime, however imperfect. Authentication has fraud-rate thresholds set by European regulators, with specific ceilings that determine whether a bank can skip the extra verification step. The merchant layer has chargeback monitoring programs like Visa’s VAMP and Mastercard’s EFM, with defined thresholds, escalation schedules, and financial penalties. The identity layer has at least conceptual assurance levels, even though they don’t travel in the payment message.
The credential layer has PCI DSS attestation. It’s binary. It’s self-assessed at most levels. And it measures whether you have the right security controls in place, not whether those controls are actually preventing card data from being stolen.
There is no public metric for how well the credential layer is actually performing. No scheme program penalizes or rewards credential-layer security the way VAMP penalizes merchants for chargebacks. No regulator publishes credential-compromise rates the way the European Banking Authority publishes fraud rates by authentication method. The credential layer is the only layer in the risk stack with no outcome measurement whatsoever.
The industry measures what it penalizes. It penalizes fraud at the merchant layer, friction at the authentication layer, and identity failure at the onboarding layer. It does not penalize credential compromise at any layer. And it does not measure the gaps between them at all.
What Five Layers Taught Us
The risk stack was not designed. It was accumulated.
Identity verification was solved by KYC providers and credit bureaus. But there’s no standard way for the result of that check, “this is a real person, we’re confident,” to travel inside the payment message when a transaction happens months or years later. The identity layer has no owner, no standard, and no way to measure whether its decisions still hold at the moment of purchase.
Merchant fraud decisioning was addressed by data-enrichment vendors and merchant data science teams. The merchant knows more about the customer than anyone else in the chain, evaluating hundreds to thousands of data points at checkout. But the payment message that reaches the bank carries only a fraction of that context. The richest signal in the chain dies at the handoff.
Authentication was solved by 3DS, the protocol that produces those “verify your purchase” prompts. The protocol is identical for every bank. But every bank is choosing which cost to absorb: fraud, conversion, or compliance. The same protocol produces radically different outcomes depending on geography and strategy.
Credential security was addressed through network-level tokenization and issuer-level dynamic credential rotation. Tokenization has a network revenue line. Dynamic CVV has an issuer cost line. There is no commercial alignment between them and no shared way to measure whether either is working.
Each layer was solved by the entity with the strongest commercial incentive to do so. None of them was built to work with the others.
That’s the pattern this series has documented across five issues. The Nilson Report trajectory that opened this series, $33.41 billion in global card fraud in 2024, heading toward $41.06 billion by 2030, is not evidence that any single layer is failing at its own job. Each layer is doing exactly what it was designed to do. The problem is that nobody designed the connections between them.
The false decline problem that opened Issue 1, $50.7 billion in refused legitimate revenue across four markets, has the same root cause. The risk stack penalizes fraud approval and ignores trust refusal. It optimizes each layer individually, resulting in an overall outcome worse than the sum of its parts. A compromised credential passes every upstream check. A legitimate customer on a flagged card range fails them. Both outcomes are produced by a stack that’s working exactly as designed. The layers aren’t bad. The system they’re supposed to be part of was never built.
Why This Matters Beyond Risk
If like me, you’ve spent your career on the optimization side of payments, on authorization rates, processing speed, interchange management, and routing efficiency, this series might have felt like a detour into someone else’s problem. It isn’t.
The payments industry has spent two decades getting extraordinarily good at processing transactions. Faster rails, smarter routing, better data, higher approval rates. That work is real, and it matters. But it was done while the risk infrastructure underneath it was accumulating without design, each layer solving its own problem, each owned by a different commercial actor, none of them measured as a system.
The professionals who only see the optimization side are missing half the picture. They’re building on a foundation they haven’t inspected. The ones who only see the risk side are missing the other half. They’re hardening layers without asking whether those layers connect to the business outcomes that pay for everything.
The companies that will navigate the next decade well are the ones that understand it’s about balance. Authorization optimization and risk architecture are not separate disciplines. There are two views of the same transaction. An approval rate means nothing if the fraud that clears it costs more than the revenue it generates. A fraud-prevention system means nothing if it refuses more legitimate customers than fraudsters. Both problems have been accelerating simultaneously, and this series has traced the structural reasons why.
EMVCo’s Digital Identity and Payments Task Force, announced in early 2026, is the most credible attempt to address the composition problem at the standards level. Visa’s Intelligent Commerce, Mastercard’s Agent Pay, and Google’s AP2 are each approaching it from their own position. These are real efforts. But they’re also, structurally, the next layers being added to a stack that has never been designed as a system.
The question this series leaves you with isn’t technical. It’s organizational. Who in your company owns the full picture, from identity to credentials, from fraud prevention to customer trust? If the answer is “different teams, different budgets, different KPIs,” you now know what that produces. You’ve seen it across five layers and five issues.
The risk stack doesn’t need better layers. It needs someone to own the system.
Thank you for reading.
This edition was made in partnership with SafeCypher, which provided its expertise, insights, and reports to help me better understand the challenges with credential security.
P.S. If reading this series made you wonder where your own authorization chain is leaking value, that’s exactly what I help institutions figure out.
20+ years in payments data and strategy. From being the First Data Scientist at Adyen, to being the First VP of Data Science & Analytics at Checkout.com, to helping over 50 of the top 150 acquirers and issuers globally, through my consultancy.
For Advisory. Speaking. Consultancy. Email me or DM me to set up a call.
Or, if you just want to keep fueling these deep dives, buy me a coffee.


Risk Mitigation is my life so this series has been great to read. Thanks!
Dwayne, as usual well done.!