The Authentication Challenge
Why the Authentication Layer is where the Issuer tests the claim the Merchant has sent.
In Australia in 2024, three percent of card spend produced 51% of card fraud. That’s the cross-border slice. Australian cardholders transacting on overseas merchants generated $454 million in CNP fraud while the domestic CNP rate sat at a record-low 97 cents per thousand dollars of spend. Same cardholders. Same issuers. Same Visa and Mastercard rails. The fraud rate moves an order of magnitude depending on which side of the border the merchant is on.
Nothing in the protocol explains that. EMV 3DS 2.x is identical for every participant. The message structure is defined the same way in Sydney and São Paulo and Singapore. The certification test plan is the same. What changes at that border is not the technology. It’s which equilibrium the issuer is positioned for.
That’s the layer this issue is about. Authentication is where the issuer tests the claim the merchant has sent. The protocol is standardized. The economics are not. And the gap between those two facts is where most of the layer’s behavior actually lives.
Where the merchant’s signal goes to be tested
The merchant holds the richest fraud-relevant context in the chain. Almost none of it travels. The thin slice that does arrives at the issuer’s authentication layer as a 3DS authentication request, and that request is where the issuer’s stack is supposed to test what the merchant has claimed.
The quality of that test is not a property of the protocol. It’s a property of the issuer’s strategic position, expressed operationally. Two issuers can receive the same request, on the same network, for the same merchant, from the same cardholder, and answer it in completely different ways. That’s not a bug. The protocol leaves the answer to the issuer.
The issue is that most issuers haven’t thought about it as an answer they’re choosing.
Authentication is not a protocol the issuer runs
EMV 3DS 2.x defines one identical message set, one SDK schema, one publicly maintained registry of approved products. Every certified ACS, every certified 3DS Server, every accredited Directory Server passes the same EMVCo test plan. The protocol leaves nothing technical to interpretation. AReq, ARes, CReq, CRes, RReq, RRes. The same on every rail.
And yet authentication outcomes vary across issuers running this identical protocol by orders of magnitude. Frictionless approval rates that range from below half to above ninety-five percent. Challenge abandonment that varies from a few percent to a third of all challenges. False challenge rates that no one can quantify because nobody measures them consistently, but that practitioners working across PSPs will tell you span ranges that no protocol could produce on its own.
The cause is choice. Each issuer is choosing how aggressively to apply exemptions, which ACS to run, which fraud model behind it, which challenge type to deploy, which fraud-versus-conversion tradeoff to live with. None of those choices are dictated by the protocol. The protocol is the same. The economics are not.
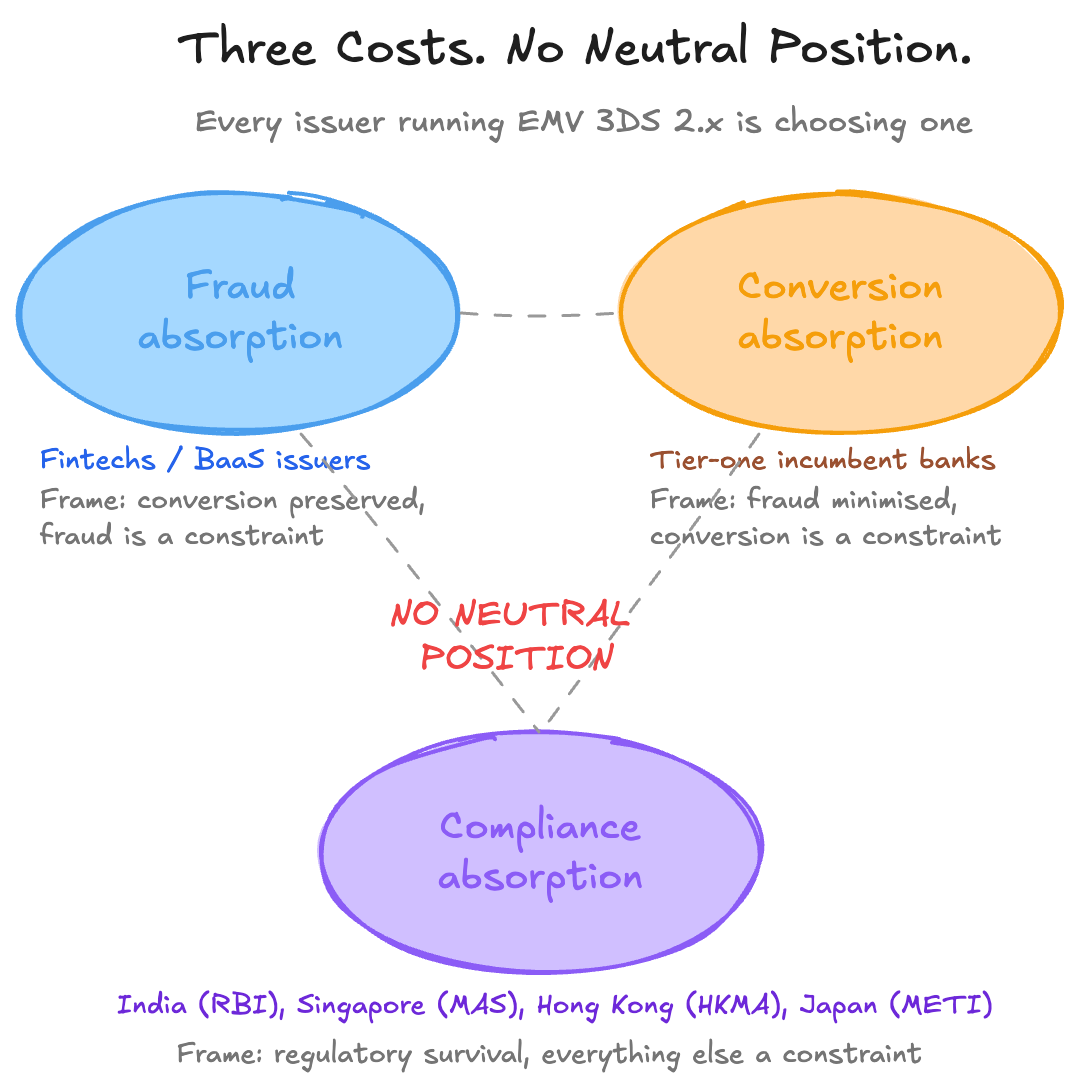
The structural argument the rest of this issue lands on is this. Authentication is where the issuer chooses which kind of cost to absorb. There are three options. There is no neutral position.
Three costs, no neutral position
The first cost is fraud absorption. The issuer accepts that some authenticated transactions will turn out to be fraudulent, treats the losses as an acquisition or retention expense, and runs a permissive authentication posture in exchange for higher conversion. Fintechs and BaaS-issued cards skew strongly toward this position. The frame is conversion preservation with a fraud constraint.
The second cost is conversion absorption. The issuer accepts that some legitimate cardholders will abandon at the challenge or be rejected by a conservative ACS, treats the revenue leakage as the price of low fraud rates, and runs a more cautious posture. Tier-one incumbent banks skew toward this position, particularly in markets where the issuer’s fraud rate is the public KPI. The frame is fraud minimization with a conversion constraint.
The third cost is compliance absorption. The issuer accepts that the regulator’s mandated factor selection or fraud-rate ceiling dictates the operational posture, and runs whatever protocol path keeps the firm out of supervisory trouble. Indian issuers post-RBI 2025, Singapore banks post-MAS digital-token mandate, Hong Kong banks post-HKMA “Authenticate in-App,” Japan post-METI all sit here. The frame is regulatory survival with everything else as a constraint.
The European Banking Authority’s reference fraud rate ladder is the cleanest single illustration that the architecture itself defines these cost lines. To apply the Transaction Risk Analysis exemption on a remote card transaction, the PSP claiming the exemption must keep its reportable fraud rate below 0.13% on payments up to €100, below 0.06% up to €250, and below 0.01% up to €500. Above €500, no TRA exemption is available at all. Those are not technical thresholds. They are cost ceilings. Whichever side of the message wants to run frictionless on more volume has to keep its fraud rate under those numbers. Whichever side runs over loses the lever.
The teams that read those numbers and the teams that bear the consequences of breaching them are usually not the same teams. The fraud team’s KPI is fraud rate. The cards team’s KPI is authorization rate and interchange. The compliance team’s KPI is no enforcement action. None of those three sees the conversion-cost-of-false-challenge that the merchant ultimately bears, because the merchant isn’t a stakeholder inside the issuer.
The ACS is a strategic asset most issuers buy as a checkbox
The Access Control Server is the issuer’s component in the 3DS flow. It receives the authentication request, decides whether to challenge, runs the challenge if needed, and returns the cryptogram. ACS quality determines latency, challenge logic, fraud detection at the authentication moment, and the user experience of the challenge itself. It is a strategic asset.
Almost no issuer builds one. Almost every issuer buys one. The vendor market splits along a legacy-versus-modern axis that maps onto the issuer-type split with surprising consistency.
On the legacy side sit Broadcom’s Arcot stack, Outseer (the carve-out of RSA’s payments authentication business), parts of the Modirum-derived deployments now consolidating under Entersekt after its December 2023 acquisition, GPayments, and the heritage on-premise deployments inside tier-one banks that were sized for 3DS 1.0 and migrated. CardinalCommerce, acquired by Visa for $300 million in December 2016, sits in this neighborhood, dominant by volume on the merchant and acquirer side rather than the issuer ACS side.
On the modern side sit G+D Netcetera, first to certify globally on EMV 3DS 2.3.1 in 2023 and deployed across more than a thousand issuers; Worldline on its modernization track; Entersekt-Modirum on its modernization track; and the BaaS-native multi-tenant entrants like Apata, Verestro and M2P, bundled into program-manager stacks for fintech and neobank issuance.
Mastercard and Visa each operate their own network ACS stand-ins for the moments when the issuer’s ACS is unavailable. Stand-in is a third category. The network answers on behalf of the issuer, and the issuer typically still bears the liability.
The ACS contract is one of the highest-leverage decisions an issuer makes about authentication. It is rarely owned by the team that owns the authorization rate. The choice locks in a fraud-versus-conversion position the rest of the issuer’s payments organization has to live with, and the team that signs the contract is usually procurement working from a vendor RFP, not the cards-P&L owner reading the operational consequences.
Exemption strategy is where the position becomes economically visible
TRA is predominantly an acquirer-side lever. The acquirer, working with the merchant, decides at the moment the authentication request is constructed whether to flag the transaction as TRA-eligible. The acquirer is the party trusting its own fraud signal enough to claim the exemption, and the acquirer is the party whose reportable fraud rate degrades if the call is wrong. The issuer holds the parallel lever on its own side of the message. Through the ACS risk-based decision, the issuer chooses frictionless approve, challenge, or decline. Both levers are forms of the same strategic choice. They sit on different sides of the authentication message.
Visa Europe has estimated publicly that 40 to 50 percent of European e-commerce by volume could qualify for TRA exemption if criteria are met. The actual frictionless rate that the layer produces sits well below that ceiling. The gap between what the regulation permits and what either side actually claims is wide.
The architecture itself adds a cruel mechanic. Under EBA Q&A 2019_4702, the issuer’s reportable fraud rate includes unauthorised transactions regardless of which side applied the exemption. If an aggressive acquirer applies TRA broadly across its merchant book and chargebacks come back, the issuer’s rate degrades on transactions the issuer never approved an exemption on. The regulator itself acknowledged the perverse incentive in the Q&A response. The issue persists. One side’s appetite for the exemption can quietly cost the other side its future ability to claim it.
The lever everyone can technically pull is one many won’t pull, because pulling it badly costs them their future ability to pull it well. Conservative posture is the safe equilibrium. The cost shows up downstream as conversion nobody traces back to authentication.
Same protocol, four different equilibria
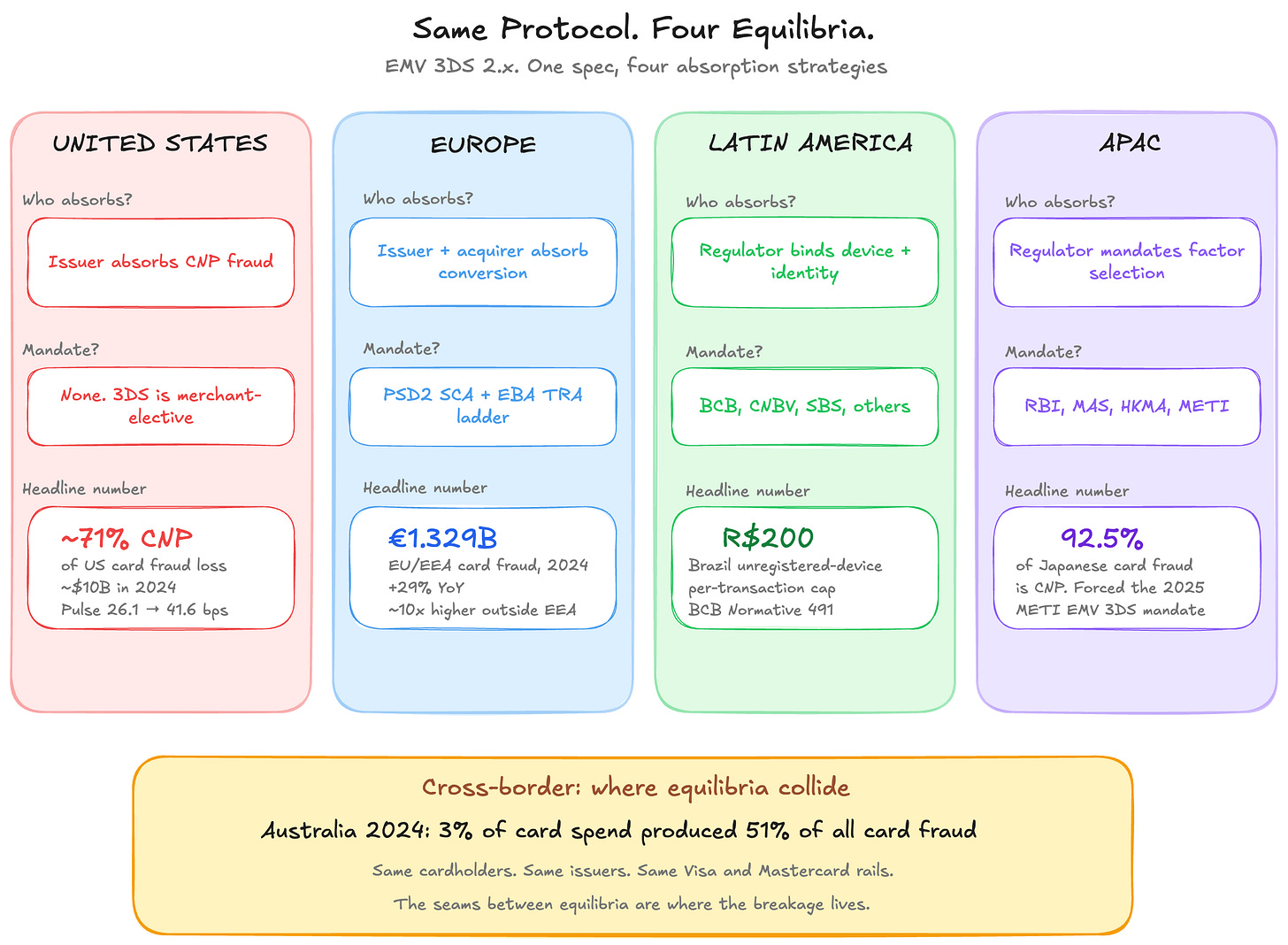
The cleanest proof that authentication is a position, not a protocol outcome, is the geographic comparison. Four major markets, the same EMV 3DS 2.x specification, four structurally different equilibria.
The United States absorbs CNP fraud at the issuer level. There is no Strong Customer Authentication mandate. 3DS adoption on US-issued cards is dramatically lower than on European-issued cards. Federal Reserve Kansas City research, in its most recent February 2026 update on 2023 Federal Reserve Board data, shows the US card-not-present fraud rate continuing its upward trend across both the dual-message networks (Visa, Mastercard, Discover) and the single-message networks (Pulse, Star, NYCE). The Pulse debit issuer benchmark CNP rate climbed from 26.1 basis points in 2019 to 41.6 basis points in 2023, and the trajectory has not reversed. Industry estimates put CNP fraud at roughly 71% of total US card fraud loss, in the neighborhood of $10 billion in 2024. The US equilibrium is issuer fraud absorption, with the merchant’s choice of whether to invoke 3DS as the only authentication lever in the system. Stripe’s analysis of US 3DS performance suggests some US issuers may treat a 3DS request itself as a fraud signal, declining 3DS-flagged transactions at higher rates than non-3DS flow because they read the request as confession of merchant suspicion. Same protocol, opposite signal interpretation.
Europe absorbs conversion at the issuer and acquirer. PSD2 SCA, the EBA Regulatory Technical Standards, the TRA exemption ladder. The 2025 EBA-ECB Joint Report on Payment Fraud documents €1.329 billion in card fraud losses across EU/EEA issuers in 2024, up 29% year over year on a base where SCA has measurably suppressed unauthorised remote fraud. The same report finds the fraud share roughly ten times higher when the counterparty sits outside the EEA, where SCA does not legally apply. The European equilibrium is conversion absorption inside the perimeter and a hard fall-off at the perimeter edge.
Latin America is converging on regulator-managed device authentication. Brazil’s central bank has issued Pix-scheme rules, Normative 491 capping unregistered-device transactions at R$200 per transaction and R$1,000 per day, and a cybersecurity package effective March 2026. Mexico’s CNBV fraud-prevention regulation took effect June 2024. Peru’s SBS Regulation 2286-2024 mandates two-factor for all card transactions. The pattern across the region is a regulator that reaches into device-binding and identity-validation rather than relying on a CNP-card SCA mandate.
Asia-Pacific is uniformly retreating from SMS OTP. India’s RBI Authentication Directions, issued September 2025, mandate two-factor for all domestic digital payments by April 2026 and risk-based controls for cross-border CNP by October 2026. Singapore’s MAS announced in July 2024 a phase-out of SMS OTP for digital-token-enabled customers. Hong Kong’s HKMA has made in-app authentication the default for online card transactions since late 2024. Japan’s METI and Japan Credit Association mandated EMV 3DS for all e-commerce as of April 2025, on a base where 92.5% of Japanese credit card fraud was CNP. Korea’s residual ARS-and-financial-certificate stack persists as the canonical example of how legacy authentication infrastructure produces structurally different friction for foreign cards.
Four regions. Same protocol. Four different answers to the question of which cost to absorb. And then there is the cross-border picture, where these equilibria collide.
When a US-issued card transacts on a European-acquired merchant, the US issuer is not bound by SCA. The merchant applies 3DS as fraud control. The issuer’s home regime governs the response. When an Indian-issued card transacts on a European merchant after October 2026, RBI’s cross-border AFA rule may require the Indian issuer to validate an Additional Factor that has no current European analogue. When an Australian cardholder transacts on an overseas merchant, the same cardholder who barely registers any CNP fraud domestically registers an order of magnitude more on the cross-border slice, because domestic and overseas authentication postures are positioned for different equilibria. The seams between equilibria are where authentication-layer breakage actually shows up.
The challenge moment is itself a strategic choice
The cardholder doesn’t see any of the protocol mechanics. The cardholder sees the moment the issuer asks them to prove they are who they say they are. Sometimes that’s a text message with a code. Sometimes it’s a fingerprint or face scan inside the bank’s app. Sometimes it’s a tap to approve. Each of those choices produces a different abandonment rate, a different fraud rate, and a different cost.
Outside the United States, regulators have stopped letting issuers make this choice freely. India’s central bank has effectively pushed banks off SMS codes. Singapore’s regulator has done the same for digital-token customers. Hong Kong has made the bank’s own app the default. Brazil and the rest of Latin America are following. The regulatory direction is uniform: SMS is not safe enough anymore, and the bank’s own app is where authentication is supposed to live.
The United States is the outlier. Most US issuers still rely heavily on SMS or no challenge at all. That’s a strategic position, even when nobody at the issuer has framed it as one.
The networks profit from heterogeneity
Visa and Mastercard each operate their own ACS stand-ins and sell network-private value-added services that wrap around the authentication moment. Mastercard’s Identity Check is the brand wrapper around its 3DS, and Smart Authentication Stand-In handles the cases where the issuer’s ACS is unavailable. Visa Authentication Suite and Visa Risk Manager play the same role on the other rail. Mastercard’s value-added services and solutions reached $3.4 billion in net revenue in the third quarter of fiscal 2025, up roughly 25% year over year, with a meaningful slice tied directly to authentication and fraud scoring. Visa’s equivalent line has grown in the high teens. Each layer of fragmentation creates a value-added service the network can sell. Mandate coherence and you commoditize the revenue.
The networks have built infrastructure around 3DS, not over it. They earn from the seams between issuers, not from closing those seams. Coherence at the authentication layer would commoditize the very services they sell to cope with the lack of coherence. The fragmentation is the business.
The measurement vacuum at the authentication layer
There’s a number nobody measures. The legitimate cardholder, challenged unnecessarily, who then abandons or fails or calls customer service or simply walks away. Call it the false challenge rate. It’s the authentication-layer cousin of the false decline, and like the false decline, it doesn’t appear on any standard report because no party in the chain has both the data and the incentive to publish it.
The issuer can sometimes infer false challenges from chargeback absence over time. The merchant sees abandonment without knowing whether the abandoner was a genuine cardholder or a fraudster who balked. The PSP sees the outcome but not the inside of the issuer’s decision. The cardholder, the only party who actually knows, is silent. There is no industry-standard metric for “challenge issued where the cardholder was the genuine cardholder, who would have completed without it.” There is no scheme report on it. There is no regulatory disclosure on it.
Which metrics an issuer chooses to optimize is itself the strategic position. An issuer watching only the chargeback rate optimizes toward conservative challenge. Every challenge issued that gets approved looks like a successful intervention even when the cardholder was genuine and would have completed without it. An issuer watching conversion-net-of-fraud optimizes toward aggressive frictionless approval. Every false challenge avoided shows up as conversion preserved. Most issuers optimize the first KPI and ignore the second, because the team that owns the second sits in a different building with a different P&L.
You can’t penalize what you can’t measure. The false-challenge tax exists because nobody with the data has the incentive to publish it.
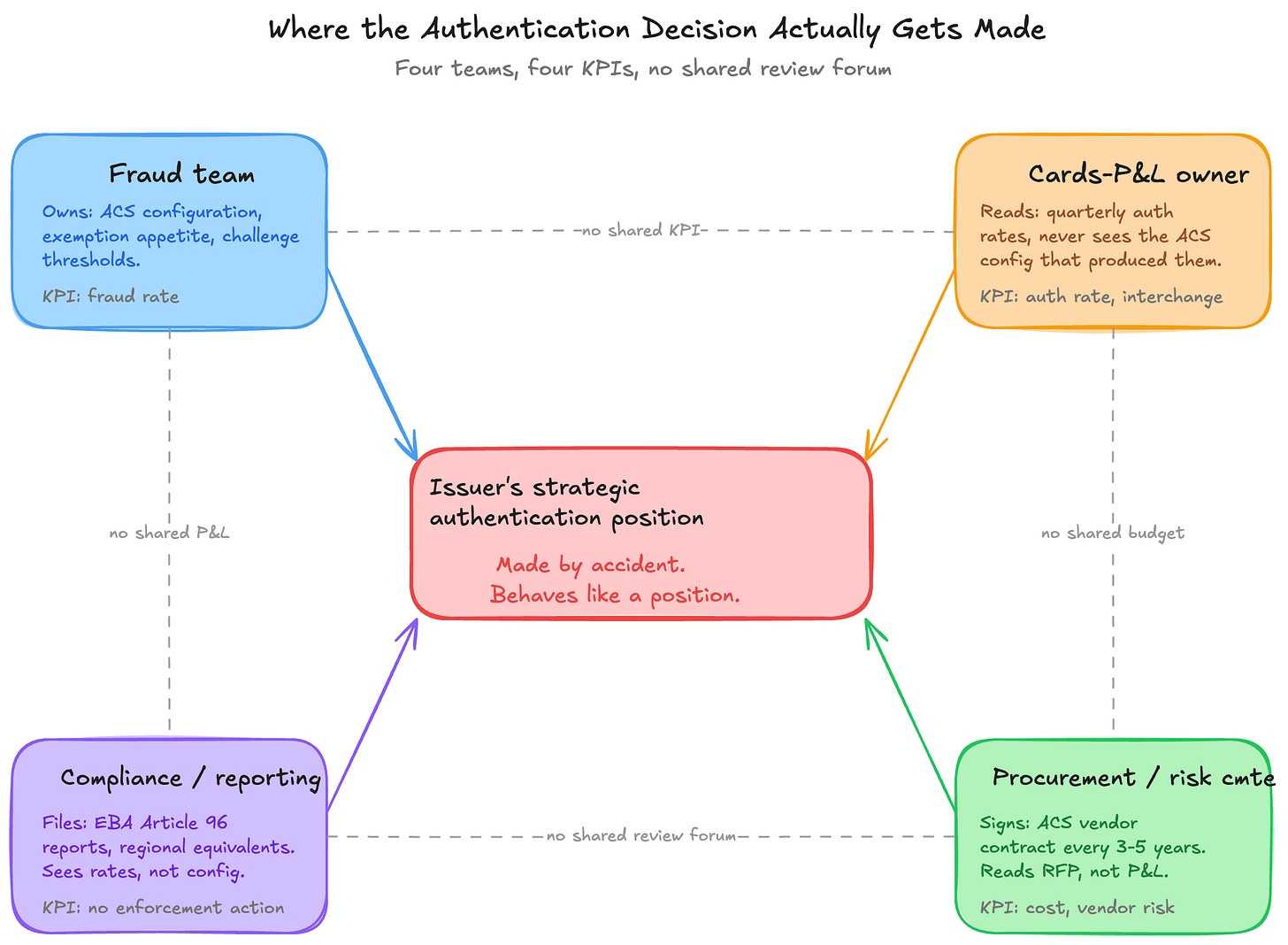
The position is mostly the residue of teams not talking
At most issuers, the strategic authentication position is not something anyone deliberately chose. It’s the operational residue of teams that don’t share P&L language.
ACS configuration is owned by the fraud team or e-banking risk. Exemption thresholds are nominally owned by fraud, but the consequence of those thresholds shows up in the cards-P&L owner’s authorization rate. EBA fraud rate reporting is owned by regulatory compliance, with data assembled from the systems the fraud team runs. The cards-P&L owner reads quarterly auth rates without seeing the ACS configuration that produced them. The fraud team reports its rate to compliance without seeing the conversion impact.
Cross-team coordination is the structural failure point. The teams collectively make the strategic position by accident. The fraud team’s appetite for false positives, the procurement team’s choice of ACS vendor three years ago, the compliance team’s interpretation of EBA Q&As, the risk committee’s tolerance for chargebacks. All of those individual decisions roll up into a strategic posture that nobody in the room ever described as a strategic posture.
This is the structural problem worth naming. Each layer inside the issuer optimizes inside its own data, its own KPI, its own reporting line. The aggregate outcome is worse than the sum of those parts. At the authentication layer, the result is a position that nobody is accountable for. The consequences look like accidents and behave like positions.
The choice is being made whether the issuer notices or not
Here’s what’s actually happening at the authentication layer. Every issuer in the world is running the same protocol. Every issuer is producing different outcomes. Those outcomes are not random and they are not technical. They are the cumulative result of choices the issuer has made about exemption appetite, ACS vendor, challenge type, fraud-rate target, and the implicit weight given to conversion against fraud against regulator. The issuer running aggressive frictionless approval, low abandonment, and a fraud rate at the EBA ceiling has chosen one position. The issuer running conservative challenge logic, higher abandonment, and a fraud rate well under the ceiling has chosen another. The issuer that defaults to scheme stand-in because its ACS is unreliable has chosen a third by accident.
The cost of the choice is paid by three different parties on three different timelines. The cardholder pays in friction. The merchant pays in conversion. The issuer pays in fraud and in regulatory exposure when the rate drifts. None of those three costs sit on the same P&L. None of them surface in the same quarterly review. None of them get reconciled in any forum where the choice could be revisited deliberately.
That is the structural challenge of the authentication layer. The decision is being made. It just isn’t being made by anyone who can see what it costs.
The next layer down is the credentials themselves. Issue 5 picks up there.
Thank you for reading.
P.S. If reading this series made you wonder where your own authorization chain is leaking value, that’s exactly what I help institutions figure out.
20+ years in payments data and strategy. From being the First Data Scientist at Adyen, to being the First VP of Data Science & Analytics at Checkout.com, to helping over 50 of the top 150 acquirers and issuers globally, through my consultancy.
For Advisory. Speaking. Consultancy. Email me or DM me to set up a call.
Or, if you just want to keep fueling these deep dives, buy me a coffee.